Securing a Kubernetes cluster is not a one-time task; it is a continuous process of hardening, monitoring, and refining. As someone who has watched the infrastructure landscape evolve from physical data centers to complex cloud-native ecosystems, I can tell you that the Certified Kubernetes Security Specialist (CKS) is currently one of the most critical benchmarks for any modern engineer. This guide is designed to help you understand the depth of the CKS, how to prepare for it, and why it is the gold standard for security in the container world.
What is the CKS Certification?
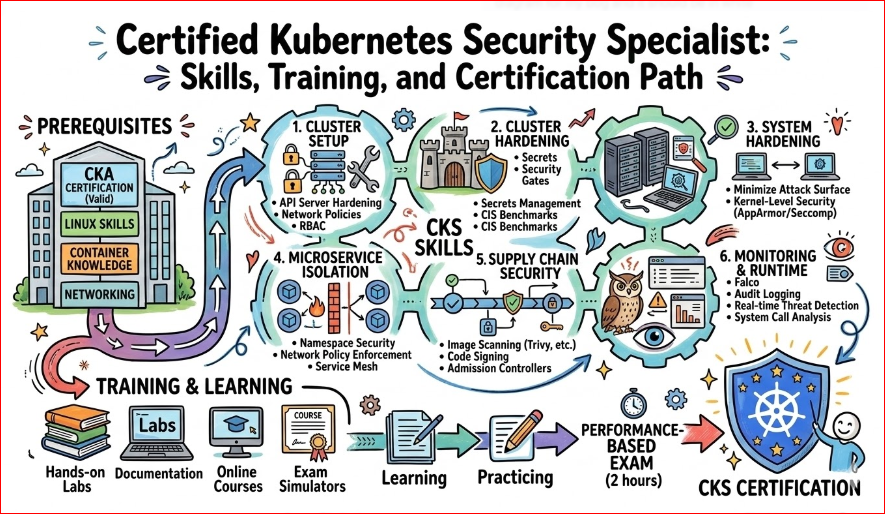
The Certified Kubernetes Security Specialist (CKS) is a performance-based certification that tests your ability to secure container-based applications and Kubernetes platforms during build, deployment, and runtime. Unlike multiple-choice exams, this requires you to solve security challenges in a live command-line environment.
Quick Overview Table
| Track | Level | Who it’s for | Prerequisites | Skills Covered | Recommended Order |
| Security | Advanced | Security Engineers, DevOps, SREs | CKA Certification | Cluster Hardening, Network Policies, Runtime Security | After CKA |
Deep Dive: Certified Kubernetes Security Specialist (CKS)
What it is
The CKS is a top-tier professional certification designed to validate an engineer’s ability to secure container-based applications across the entire cloud-native lifecycle. It moves beyond simple administration to focus on advanced defense mechanisms, such as cluster hardening, vulnerability reduction, and active threat detection. Holding this credential proves you can handle the high-stakes responsibility of protecting production-grade Kubernetes environments from sophisticated attacks.
Who should take it
This certification is tailor-made for experienced System Administrators, DevOps Engineers, and Security Professionals who have already mastered the basics of Kubernetes. It is particularly valuable for those working in highly regulated industries like FinTech, Healthcare, or Government, where security compliance is non-negotiable. If you are responsible for designing “Zero Trust” architectures or managing multi-tenant clusters, this is the definitive benchmark for your skills.
Skills you’ll gain
- Cluster Hardening: You will learn to secure the API server, implement strict Role-Based Access Control (RBAC), and protect the etcd database from unauthorized access.
- System Hardening: Gain the expertise to minimize host OS vulnerabilities using kernel-level tools like AppArmor and Seccomp profiles to restrict container capabilities.
- Microservice Security: Master the implementation of Pod Security Admissions and sophisticated Network Policies to isolate sensitive workloads and prevent lateral movement.
- Supply Chain Security: Learn to verify image integrity, scan for vulnerabilities in CI/CD pipelines, and use Admission Controllers to block untrusted code from running.
- Monitoring & Logging: Develop the skills to detect runtime threats and suspicious activity in real-time using auditing and behavioral analysis tools like Falco.
Real-world projects you can do after it
- Automated Vulnerability Shield: Design a pipeline that automatically blocks the deployment of any container image containing critical CVEs or outdated libraries before it reaches production.
- Zero-Trust Networking: Architect a cluster-wide policy where pods can only communicate with specific services, effectively stopping hackers from moving through your network during a breach.
- Intrusion Detection System: Deploy and tune a runtime security engine to alert your team immediately if an unauthorized shell or process starts in a production environment.
- Compliance Auditing: Create an automated reporting system that checks your cluster configuration against CIS Benchmarks to ensure continuous security compliance for audits.
Preparation plan (30 days – Recommended)
- Phase 1 (Days 1-10): Focus on the foundations of Cluster Hardening and System Security, ensuring you can navigate the Linux CLI to modify API server flags and host configurations.
- Phase 2 (Days 11-20): Deep dive into the “Supply Chain” and “Microservices” domains, practicing with tools like Trivy for scanning and OPA Gatekeeper for policy enforcement.
- Phase 3 (Days 21-30): Dedicate this time to Runtime Security and mock exams, focusing on speed and accuracy in troubleshooting security misconfigurations under a strict time limit.
Common mistakes
- Ignoring the CKA Foundation: Many candidates struggle because they haven’t refreshed their CKA skills; remember, you must know how to fix a broken cluster before you can secure it.
- Slow Documentation Search: The exam environment is timed, and relying too heavily on the official docs without knowing exactly where to look will lead to a “did not finish” result.
- Overlooking the Host OS: It’s easy to focus only on YAML files, but CKS requires you to understand the underlying Linux nodes, including SSH hardening and kernel security modules.
- Poor YAML Formatting: In a high-pressure environment, small indentation errors can break a security policy; always double-check your syntax before applying changes to the cluster.
Best next certification after this
Once you have conquered the CKS, the natural progression is to specialize in the broader DevSecOps ecosystem or a specific cloud provider’s security stack. The Certified DevSecOps Professional (CDP) is an excellent choice to learn about security outside of Kubernetes, while an AWS/Azure Security Specialty allows you to master the proprietary tools offered by major vendors. For those moving into leadership, the CISSP remains the gold standard for high-level security management and risk assessment.
Choose Your Path: 6 Learning Tracks
Depending on your career goals, the CKS fits into different professional journeys:
- DevOps Path: Focuses on integrating security early into the CI/CD pipeline, ensuring that speed does not come at the cost of vulnerability.
- DevSecOps Path: The “Deep Dive” where CKS is the core pillar of a comprehensive security strategy that covers code, cloud, and containers.
- SRE Path: Focuses on how security incidents affect reliability and uptime, using CKS skills to build resilient systems that withstand attacks.
- AIOps/MLOps Path: Securing the massive data pipelines and GPU workloads running on K8s that power modern artificial intelligence models.
- DataOps Path: Protecting sensitive data at rest and in transit within containerized databases and ensuring strict access control for data scientists.
- FinOps Path: Ensuring that security tools and monitoring agents are optimized so they don’t inflate cloud costs or consume unnecessary cluster resources.
Role → Recommended Certifications
| Your Current Role | Recommended Certifications Mapping |
| DevOps Engineer | CKA → CKS → HashiCorp Vault |
| SRE | CKA → CKS → Chaos Engineering |
| Platform Engineer | CKA → CKAD → CKS |
| Cloud Engineer | AWS/Azure/GCP Architect → CKS |
| Security Engineer | CKS → CISSP → Certified Ethical Hacker |
| Data Engineer | CKA → CKS → Databricks/Snowflake Security |
| FinOps Practitioner | FinOps Certified Practitioner → CKS (Cost Security) |
| Engineering Manager | CKA (Generalist) → CKS (Risk Management focus) |
Where to Get Training
- DevOpsSchool: This institution stands out for its hands-on approach, providing learners with real-world lab environments that mimic actual production failures. Their instructors bring decades of industry experience, ensuring that students don’t just pass the exam but actually learn how to solve complex security puzzles.
- Cotocus: Known for its intensive bootcamps, Cotocus focuses on the “performance” aspect of the CKS exam, offering drills that improve speed and CLI proficiency. Their curriculum is updated frequently to reflect the latest Kubernetes releases and security trends, making it ideal for engineers who need to get certified quickly.
- Scmgalaxy: This platform is a treasure trove of community-driven knowledge, offering extensive blogs, tutorials, and open-source contributions. It is perfect for self-starters who want to understand the integration of security tools within the wider DevOps lifecycle and CI/CD pipelines.
- BestDevOps: This site offers specialized training modules that bridge the gap between theoretical knowledge and enterprise application. They focus heavily on how security impacts business outcomes, making their training highly relevant for senior engineers and aspiring architects.
- Specialized Schools: For niche tracks, you can explore devsecopsschool.com, sreschool.com, aiopsschool.com, dataopsschool.com, and finopsschool.com for role-specific security training tailored to your exact career path.
FAQs (Certified Kubernetes Security Specialist)
1. Is the CKS exam harder than the CKA?
Yes, most professionals consider it a significant step up in difficulty. While CKA tests your ability to build and maintain a cluster, CKS requires you to find and fix vulnerabilities, which demands a more analytical and “attacker-mindset” approach.
2. What is the most important skill for the CKS exam?
Speed and familiarity with the Linux command line are paramount. Since it is a performance-based exam, you must be able to edit configuration files, restart services, and navigate the official Kubernetes documentation extremely quickly.
3. Do I really need to be a CKA to take the CKS?
Yes, the Linux Foundation strictly requires a valid CKA certification as a prerequisite. This ensures that every candidate has a baseline understanding of cluster administration before tackling advanced security concepts.
4. How many questions are on the CKS exam?
The exam typically consists of 15 to 20 lab-based tasks that you must complete within two hours. Each task carries a different weight, and you must manage your time carefully to ensure you hit the 67% passing threshold.
5. Can I use external tools like Helm during the exam?
You are generally expected to use the native Kubernetes tools and specific security binaries (like Falco or Trivy) mentioned in the curriculum. While some clusters might have Helm installed, the focus is on manual configuration and understanding the underlying manifests.
6. What happens if I fail the first attempt?
Most exam vouchers purchased through the Linux Foundation or authorized partners like DevOpsSchool include one free retake. This allows you to identify your weak areas during the first try and return better prepared.
7. How does CKS benefit my career in India vs. globally?
Globally, CKS is recognized as a premier credential for high-paying Security Engineer roles. In India’s rapidly growing tech hubs, it distinguishes you from thousands of general DevOps engineers, often leading to roles in global MNCs and specialized security firms.
8. Are third-party security tools like Falco and Trivy covered?
Yes, a core part of the CKS involves installing, configuring, and interpreting the output of these tools. You will be expected to write Falco rules and analyze image scan results to determine if a container is safe for production.
Frequently Asked Questions (CKS Certification)
1. How difficult is the CKS compared to the CKA? The CKS is widely considered one of the most challenging certifications in the cloud-native ecosystem. While the CKA tests your ability to build and maintain a cluster, the CKS requires you to find and fix deep-seated vulnerabilities under significant time pressure. It demands a “security-first” mindset and a much deeper understanding of the Linux kernel and third-party security tools.
2. What is the mandatory prerequisite for taking the CKS exam? You must hold a valid, non-expired Certified Kubernetes Administrator (CKA) certification to attempt the CKS. This ensures that every candidate has a strong foundation in cluster administration and troubleshooting before moving into advanced security hardening. If your CKA expires, you lose the eligibility to sit for the CKS until you recertify.
3. What is the ideal sequence for Kubernetes certifications? The most logical and effective path is to start with the CKA (Administrator) to understand the architecture, followed immediately by the CKS (Security) while the CLI commands are fresh in your mind. Some choose to take the CKAD (Developer) first to get comfortable with the exam environment, but for infrastructure roles, the CKA-to-CKS transition is the standard.
4. How much time should I dedicate to preparation? For a working professional already familiar with Kubernetes, 30 to 45 days of consistent study (roughly 10–12 hours per week) is usually the sweet spot. If you are new to security concepts like Falco or OPA, you may want to extend your timeline to 60 days to ensure you can configure these tools manually without relying on external guides.
5. What is the format of the exam? The CKS is a 100% performance-based exam conducted in a virtual lab environment via a web browser. You are given 15 to 20 real-world tasks that you must complete within 120 minutes. There are no multiple-choice questions; you are judged solely on your ability to implement security configurations in a live terminal.
6. Is the CKS certification worth the investment? Absolutely. As organizations move more sensitive workloads to the cloud, the demand for “DevSecOps” expertise has skyrocketed. The CKS is a premium credential that signals to employers that you can protect their infrastructure against modern threats, often leading to faster promotions and access to high-stakes projects.
7. How does the CKS impact career outcomes and salary? Engineers with CKS certification often see a significant increase in marketability, particularly for Senior DevOps, Security Engineer, and Platform Architect roles. In major tech hubs, having “CKS” on your resume can command a salary premium of 20% to 30% compared to those with only basic Kubernetes certifications.
8. Can I use the official documentation during the test? Yes, you are allowed to open one additional browser tab to access the official Kubernetes documentation, the Kubernetes blog, and specific documentation for tools like Falco, AppArmor, and Trivy. However, the time limit is strict, so you must know exactly what to look for rather than learning on the fly.
9. What are the most common reasons people fail the CKS? The primary reasons for failure are poor time management and a lack of speed with the Linux command line. Many candidates also struggle with YAML indentation errors or failing to restart the Kubelet after making changes to the API server, which can result in the entire cluster becoming unreachable.
10. How long is the CKS certification valid? The CKS certification is valid for a period of 2 years from the date you pass the exam. To maintain your status, you will need to retake the exam before the expiration date, which ensures you stay up-to-date with the rapidly evolving security features in the Kubernetes ecosystem.
11. Does the CKS cover cloud-specific security tools? No, the CKS focuses on “distribution-neutral” security. This means you are tested on open-source tools and native Kubernetes features that work regardless of whether you are on AWS, Azure, GCP, or on-premise. This makes your skills highly portable across different cloud providers.
12. What kind of value does this bring to an Engineering Manager? For managers, having a CKS-certified team—or being certified yourself—drastically reduces the risk of production breaches and data leaks. It provides a common language for security and operations, ensuring that your team builds “secure by design” systems that satisfy even the most rigorous compliance audits.
Testimonials
“Transitioning from traditional ops to cloud-native security was daunting. The CKS training at DevOpsSchool gave me the practical confidence to secure our banking production clusters.” — Aman S.
“The CKS isn’t just a paper certificate; it’s a rite of passage. It changed how I view container networking and image safety, making me a much more valuable asset to my team.” — Sarah L.
Conclusion
The Certified Kubernetes Security Specialist (CKS) is more than just a credential; it is a signal to the industry that you can protect business-critical infrastructure. As we move further into a world of automated threats, the ability to harden a cluster, scan for vulnerabilities, and monitor runtime behavior is no longer optional—it is essential. Whether you are an engineer looking to level up or a manager building a secure team, the CKS is the path forward to a safer cloud-native future.